Sangfor Endpoint Secure
Comprehensive Endpoint Security Solution
Sangfor Endpoint Secure takes a unique approach to defending against malware and APT threats, offering a significant evolution from traditional next-generation Anti-Virus (NGAV) and Endpoint Detection & Response (EDR) solutions.
Endpoint Secure delivers an organization-wide response to malware infections and APT breaches, ensuring seamless management, operation, and maintenance. This scalable solution caters to organizations of all sizes, providing options for on-premise, cloud-based, or hybrid management to address endpoint security, protection, detection, and response effectively.
What is Endpoint Security?
Endpoint security refers to the practice of protecting devices such as desktops, laptops, servers, and mobile devices from cyber threats. It involves implementing solutions that detect, prevent, and respond to attacks targeting these endpoints, safeguarding an organization’s network and critical assets.
Sangfor Endpoint Security Overview
Pre-Attack Prevention
Sangfor Endpoint Secure offers comprehensive pre-attack prevention capabilities to proactively protect against potential threats. These include:
Endpoint Discovery & Unified Endpoint Management: Gain complete visibility and control over all endpoints in your network, ensuring secure and centralized management.
Vulnerability & Patch Management: Identify vulnerabilities across endpoints and deploy timely patches to eliminate security gaps before they can be exploited.
Configuration Baseline Check: Enforce standardized security configurations across endpoints to minimize risks and maintain a secure operating environment.
During Attack
Passive Detection
Sangfor Endpoint Secure employs advanced detection mechanisms to identify threats during an attack:
Signature-Based Detection (Traditional AV): Uses known threat signatures for quick and effective identification of familiar malware.
Behavior-Based Detection (NG-AV): Monitors anomalous behaviors indicative of advanced threats.
AI & Machine Learning (NG-AV): Leverages AI-driven algorithms to detect previously unknown threats with precision.
Sandboxing (NG-AV): Isolates and analyzes suspicious files in a controlled environment to uncover malicious intent.
Active Protection
In addition to detection, Endpoint Secure provides robust active defense measures to mitigate threats:
Micro-Segmentation: Limits lateral movement within the network by isolating compromised endpoints.
Ransomware Honeypot: Deceives and traps ransomware attacks to prevent data encryption.
Two-Factor Authentication: Strengthens endpoint security by adding an extra layer of identity verification.
Brute-Force Attack Detection: Identifies and mitigates brute-force attempts to compromise endpoints.
Residual Threat Detection
Sangfor Endpoint Secure ensures that no threats linger after an attack by employing advanced detection capabilities:
Threat Hunting: Actively searches for hidden threats or undetected vulnerabilities within the network.
Forensic Analysis: Conducts detailed investigations to identify the attack’s origin, entry points, and affected assets.
Threat Correlation & Visualization
The platform consolidates and correlates threat data from multiple sources, presenting it through intuitive visualizations. This enables security teams to gain a comprehensive understanding of the attack chain and take decisive actions for remediation.
Sangfor Endpoint Secure Key Capabilities
Phishing and Web Intrusion Protection
Sangfor Endpoint Secure provides advanced protection against phishing and web intrusion attacks with accurate detection and detailed visual kill chains to trace origins. Automated responses can terminate malicious processes and delete files, preventing lateral movement and ensuring swift containment.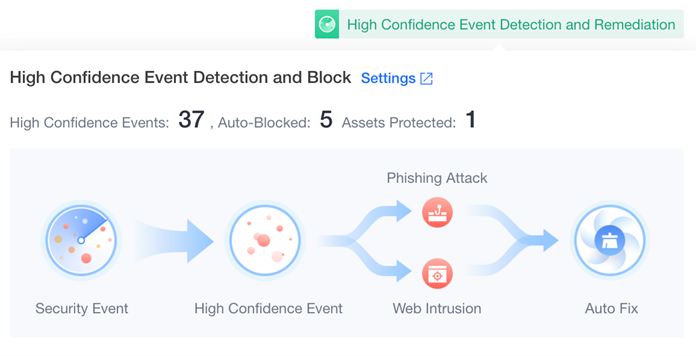
Ransomware Protection and Recovery
Sangfor Endpoint Secure defends against ransomware with AI-powered detection, blocking suspicious processes within 3 seconds and achieving 99.83% detection accuracy. It collects ransomware indicators from over 12 million devices and offers recovery features, including file restoration and VSS snapshot backup, ensuring data security and swift restoration post-attack.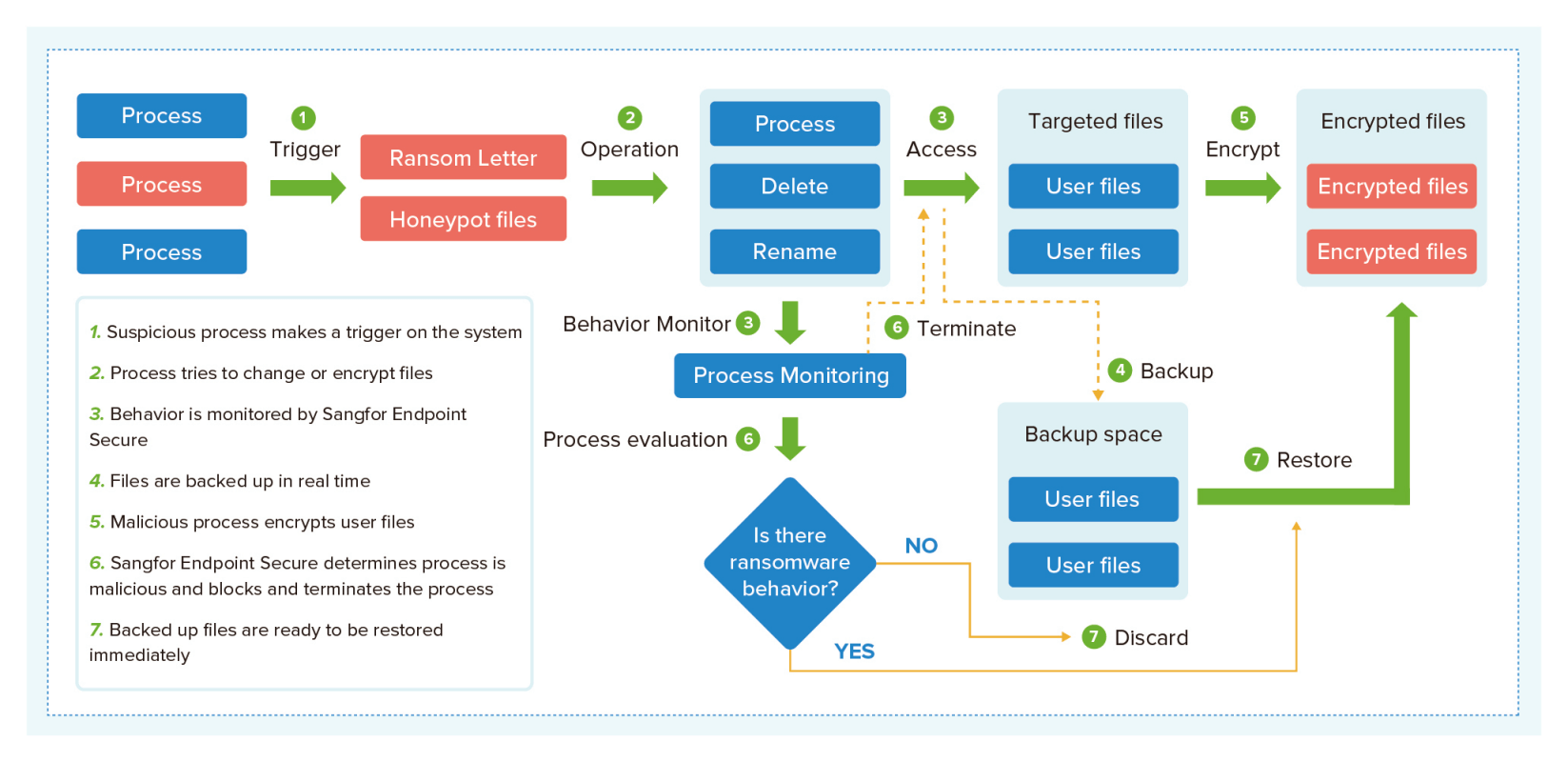
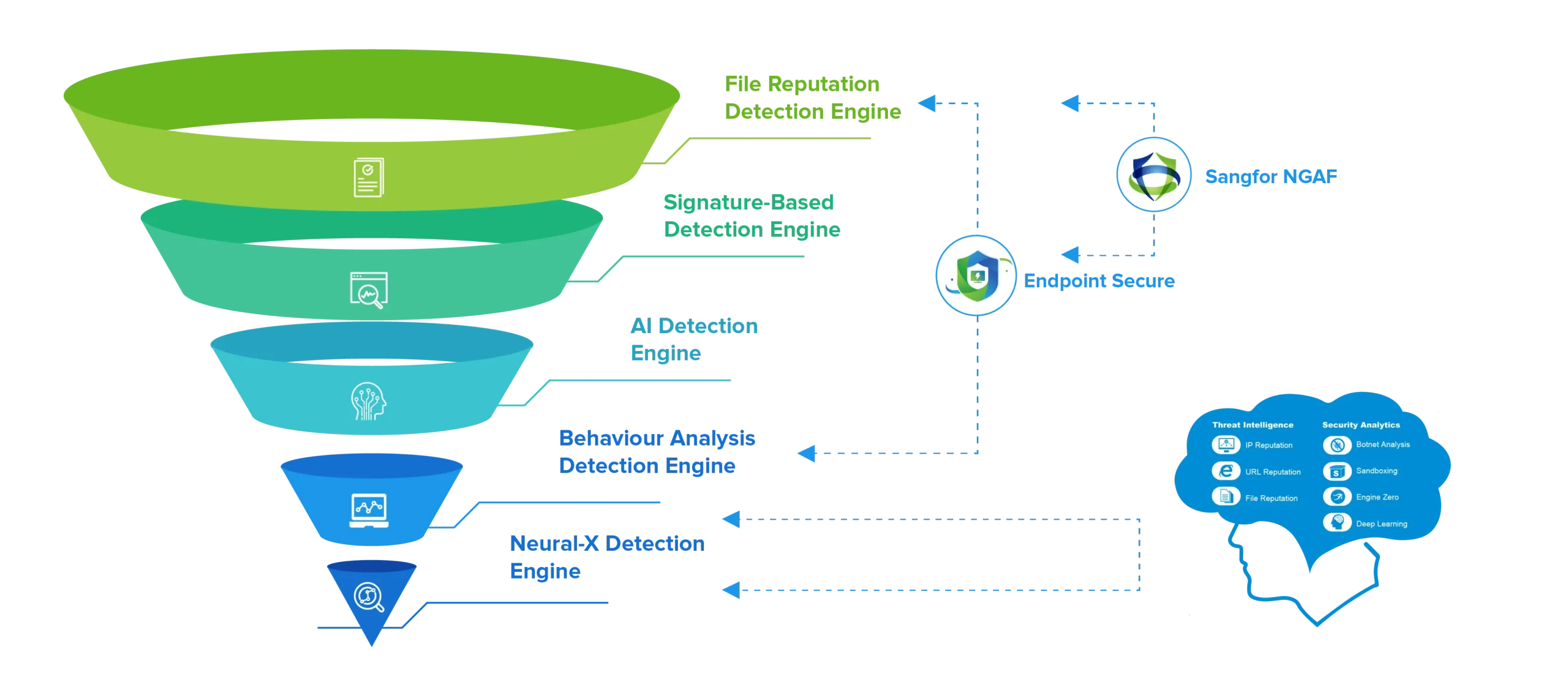
Synergy with Network and Cloud
Sangfor Endpoint Secure seamlessly integrates with NGAF, IAG, and Cyber Command to enable unified threat detection and response. This synergy correlates threats across endpoints, networks, and cloud environments, uncovering advanced threats missed by isolated solutions and streamlining post-attack analysis and remediation with an integrated evidence chain.
World-Class Malware Detection
Ransomware Attack Trends
Ransomware Protection
Sangfor offers customizable ransomware solutions, combining Endpoint Secure with add-ons like NGAF or HCI backup. These solutions are flexible, catering to various needs and budgets, and include cloud-based security management through Platform-X.
Ransomware Protection
Sangfor offers customizable ransomware solutions, combining Endpoint Secure with add-ons like NGAF or HCI backup. These solutions are flexible, catering to various needs and budgets, and include cloud-based security management through Platform-X.
Cost-Effective Endpoint Protection
Sangfor Endpoint Secure reduces TCO by up to 60% with simplified operations through Platform-X cloud management. Integration with Sangfor NGAF enhances breach response time by up to 40%.
Frequently Asked Question
Can I install the Endpoint Secure Protect Agent on a system already running AV or EDR?
Endpoint Secure Protect can be installed alongside existing AV or EDR solutions. During installation, selecting compatibility mode automatically disables real-time protection to avoid conflicts with the existing AV agent, ensuring smooth operation.
What protection mechanisms are deployed with the management server?
The Endpoint Secure management server integrates the NGAF WAF module to block web-based attacks. Sangfor’s BlueSecOps Team conducts thorough risk assessments and applies security hardening by disabling unnecessary ports and services, reducing attack surfaces
Can I choose when agents are upgraded to minimize network impact?
You can schedule agent group or individual agent upgrades, providing the flexibility to stagger or delay updates based on your organization’s requirements.
